threat-trace
agentic defense, in your browser
A working multi-agent log-analysis pipeline. One self-contained HTML file. No install, no server, no telemetry. Walk it in fifteen minutes.
The attackers running coordinated campaigns against your stack right now are multi-step, multi-stream, adaptive. They probe the edge, pivot to the identity tier when the WAF slows them down, rotate IPs, exploit legacy allowlists DevOps quietly accepted years ago. They orchestrate.
Defenders' AI tooling is mostly: paste a log into a chat AI, ask "what stands out?" That's a single-completion analyst on a specialty task. It's not a defense system. It misses the bypasses (one stream looks clean, another floods without context, the truth lives between them). It hallucinates correlations (two unrelated 4xx events in the same time window get bundled into the wrong narrative). It can't show its work in a post-mortem.
threat-trace is what the composed-signals version looks like. Three log streams under attack — an edge tier (CDN / WAF), an identity tier (logins), an api tier (application traffic). Three discrete agents reasoning over each stream in isolation. A cross-stream layer that correlates them. A load-bearing negative check: two routine token-expiration 401s in the api tier must not be lumped in with the unrelated password spray happening at the same time. A naïve scanner walks straight into that trap. The pipeline catches it; the expectation panel says so out loud.
The fixture data ships in three well-documented public log shapes (Cloudflare GraphQL Analytics for the edge tier, Auth0 tenant logs for the identity tier, Azure App Insights AppRequest for the api tier) because those are the most reviewable starting points. The parser contract is vendor-agnostic — swap in Fastly / Akamai / CloudFront, Okta / Cognito / Keycloak / Entra ID, or OpenTelemetry-style application logging without touching anything above the parsers.
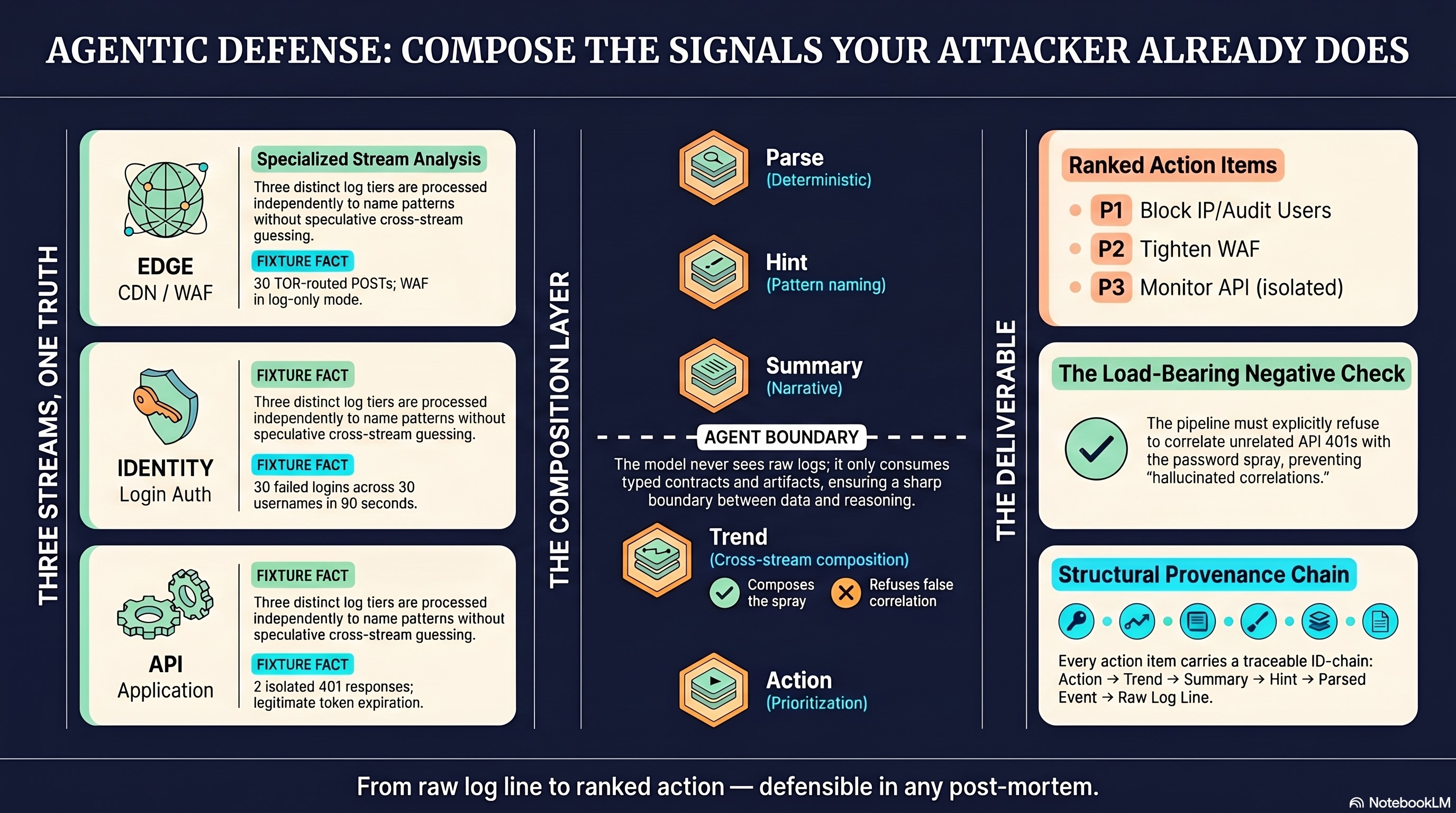
Every recommended action carries its evidence chain back to the specific raw log lines that justified it. Click any action item; walk the chain. Defensible in a post-mortem, not just a demo.
This is given away because everyone running a stack against the modern bot wave should already have one. Building it isn't the hard part — knowing it needs to exist is. So the working pattern, complete, ships here, with every seam visible. Take it. Fork it. Fold it into your stack. Replace the synthetic fixture with your own log shapes. The handoff guide that ships with the source has prompts an engineer can paste into Claude Code or Cursor to extend the pipeline one slice at a time.
No API key needed for Phase 1 (free, copy-paste through any chat AI). Bring an Anthropic API key for Phase 2 (pennies per run, automated). The key lives in browser memory only — never written to disk, never exported.